Join ML Engineer Interview MasterClass (June Cohort) led by FAANG Data Scientists | Just 6 seats remaining...
ML Engineer MasterClass (June) | 6 seats left
Consistent Hashing
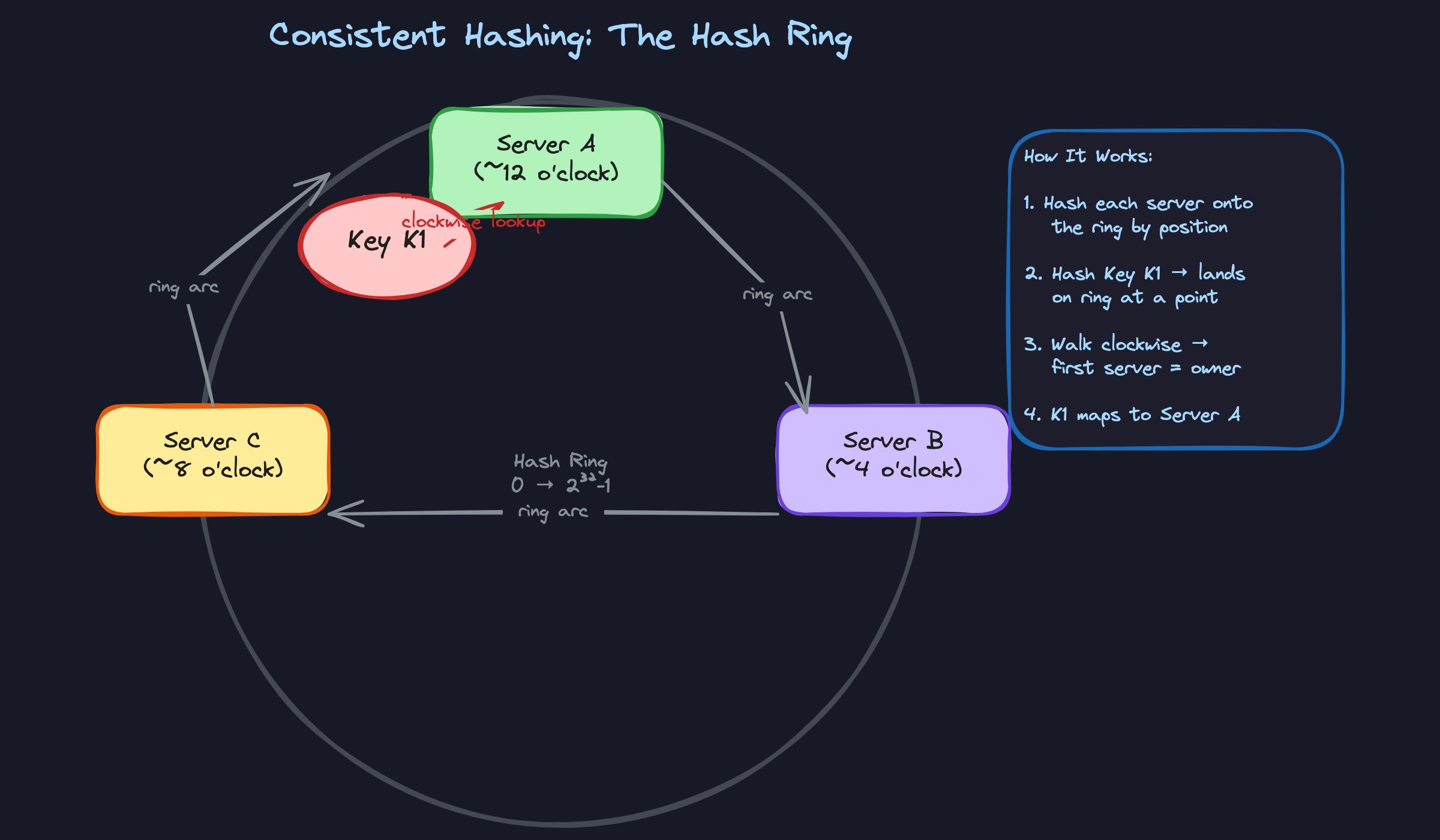
The Hash Ring
When Amazon's Dynamo paper dropped in 2007, one idea inside it quietly changed how distributed systems get built: consistent hashing. Not because it's mathematically elegant (though it is), but because it solves a failure mode that breaks naive implementations completely. Remove one node from a four-server cluster using key % 4, and you're now running key % 3. Almost every key remaps to a different server. Your cache hit rate collapses. Your database absorbs a thundering herd of requests that were supposed to be cached. The system survives, barely, but the damage is real.
Consistent hashing fixes this by putting both servers and keys on the same conceptual circle. Each key walks clockwise around that circle until it finds a server. When a node disappears, only the keys it owned shift to the next server clockwise. Everything else stays put. Instead of remapping nearly all your keys, you remap roughly 1/N of them. Cassandra uses this for partition placement. Akamai uses it to route CDN requests to edge servers. Memcached clusters use it to survive node failures without a full cache flush. Drop one of those names in your interview and you signal that you've seen this in the wild, not just on a whiteboard.
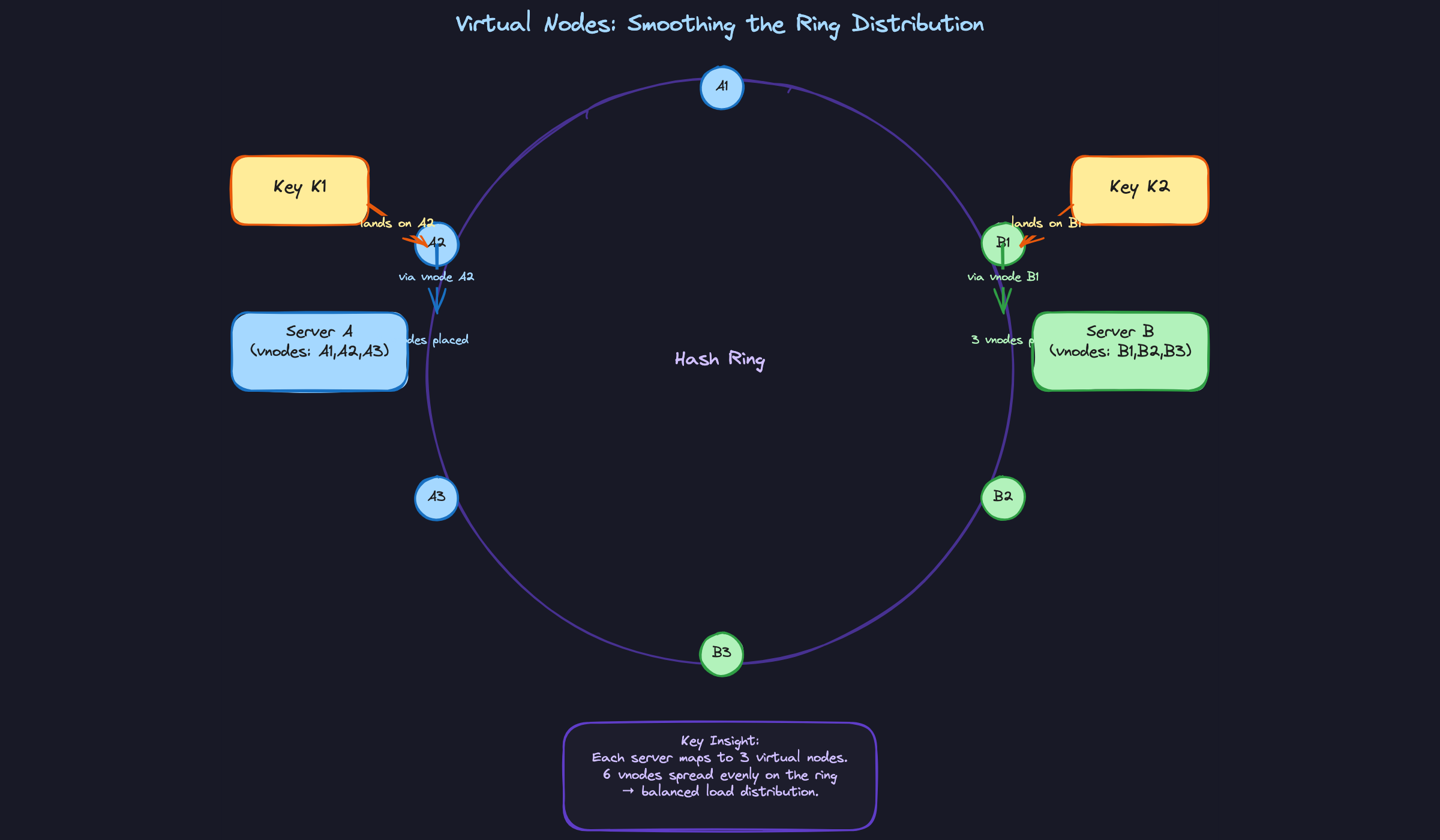
The concept has one sharp edge that interviewers love to probe: naive consistent hashing creates uneven load distribution. That's where virtual nodes come in, and that's where most candidates lose points. Knowing the ring is step one. Knowing why the ring alone isn't enough is what separates a good answer from a great one.
How It Works
Think of a clock face, but instead of 12 hours, it has about 4.3 billion positions (0 to 2^32-1), and the numbers wrap around so that the position after the maximum loops back to zero. That's your hash ring.
Both servers and keys get hashed onto this same ring. You take a server's identifier (its IP address, hostname, whatever) and run it through a hash function like SHA-1 or MD5 to get a position on the ring. You do the exact same thing with your data keys. Everyone lives in the same circular space.
To figure out which server owns a key, you start at the key's position and walk clockwise until you hit the first server. That's it. That's the entire lookup algorithm.
Walking Through a Concrete Example
Let's place four servers on the ring. After hashing their identifiers, they land at these positions:
- Server A lands at position 10
- Server B lands at position 75
- Server C lands at position 150
- Server D lands at position 220
Now hash three keys. Key K1 ("user:alice") hashes to position 60. Key K2 ("user:bob") hashes to position 160. Key K3 ("user:carol") hashes to position 5.
K1 sits at position 60. Walk clockwise from 60, and the first server you hit is Server B at 75. So Server B owns K1.
K2 is at 160. Walk clockwise, pass nothing until you reach Server D at 220. Server D owns K2.
K3 is at position 5. Walk clockwise and you immediately bump into Server A at 10. Server A owns K3.
Here's what that flow looks like:
When a Node Dies
Server C crashes. What happens?
Only the keys that lived in the arc between Server B (position 75) and Server C (position 150) need to move. Those keys were walking clockwise and landing on Server C. Now that Server C is gone, they keep walking and land on the next server clockwise: Server D.
K1 at position 60? Still walks clockwise to Server B. Unchanged. K3 at position 5? Still hits Server A. Unchanged. The only keys affected are the ones that specifically belonged to the dead node. Everything else stays exactly where it was.
With four servers, roughly 1/4 of the keys need to remap. Not all of them. Compare that to modular hashing, where removing one server (going from key % 4 to key % 3) scrambles the assignment of nearly every single key.
When a Node Joins
A new Server E joins and hashes to position 100, right between Server B (75) and Server C (150).
Server E now "absorbs" the keys in the arc from position 75 to 100. Those keys used to walk clockwise past 75 and land on Server C at 150. Now they hit Server E at 100 first. Server C keeps the keys between 100 and 150. Everyone else on the ring is completely unaffected.
Again, only a fraction of keys move. If you had 100 servers and added one more, roughly 1/100th of the data migrates. In the modular hashing world, going from key % 100 to key % 101 reshuffles almost everything, which means cache misses everywhere, rebalancing storms, and a very bad day for your on-call engineer.
Properties Your Interviewer Cares About
Minimal disruption. When the cluster changes size, only O(K/N) keys move, where K is the total number of keys and N is the number of servers. This is the single most important property. If you explain nothing else, explain this. Interviewers ask about node failures and scaling events specifically to see if you understand that consistent hashing keeps the blast radius small.
Decentralized lookups. Any client that has a copy of the ring can independently determine which server owns a key. There's no central routing authority that becomes a bottleneck or single point of failure. This matters when the interviewer pushes you on how your system handles high throughput; the lookup itself is just a hash plus a sorted search.
Deterministic placement. Given the same hash function and the same set of nodes, every client will agree on where every key lives. No coordination needed. This is why it works so well for distributed caches and partitioned databases, where clients need to independently agree on ownership without talking to each other.
Patterns You Need to Know
In an interview, you'll usually need to pick a specific approach. Here are the ones worth knowing.
Virtual Nodes
Place only 3 or 4 physical servers on a hash ring and you'll immediately see the problem: the arcs between them are wildly uneven. One server might own 50% of the key space while another owns 10%. That's not a theoretical concern; it means one machine is fielding five times the traffic of its neighbor.
Virtual nodes fix this by giving each physical server many positions on the ring instead of one. Server A becomes A1, A2, A3 … A150. Server B becomes B1, B2, B3 … B150. Now instead of 4 points on the ring, you have 600, and the arcs between them shrink toward uniform. A key still walks clockwise to the nearest point, but that point maps back to a physical server through a simple lookup table. In practice, 100 to 200 virtual nodes per server gets you within a few percent of perfectly even distribution.
When to reach for this: virtually always. Any time you draw a consistent hash ring in an interview, virtual nodes should be your default. The basic ring without them is just the setup for explaining why vnodes exist.
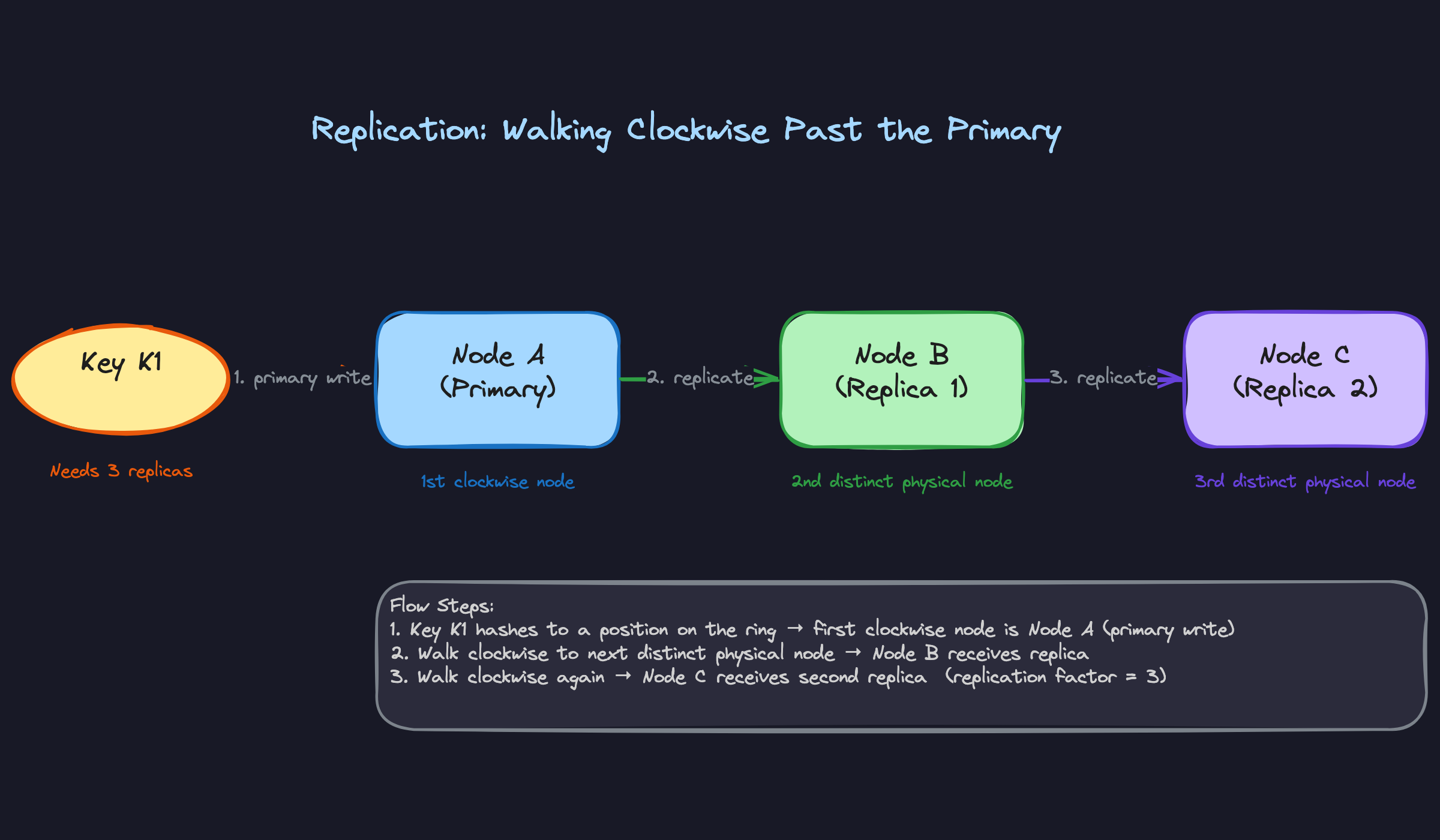
Replication on the Ring
Your data can't live on a single node. Nodes die. So once a key finds its primary server by walking clockwise, you keep walking and place replicas on the next N distinct physical nodes. If your replication factor is 3, the key ends up on three separate machines.
Here's where virtual nodes make things tricky. Walking clockwise, the next point on the ring might be another vnode belonging to the same physical server you just placed a replica on. That doesn't help your fault tolerance at all. So the replication logic has to skip vnodes until it finds a point owned by a different physical machine. Cassandra does exactly this with its token-aware replication strategy, and it's a detail interviewers love to hear because it shows you understand the interaction between two concepts, not just each one in isolation.
When to reach for this: any design where durability or availability matters (so, basically every design). The moment you mention consistent hashing for a database or storage system, replication placement on the ring should follow naturally.
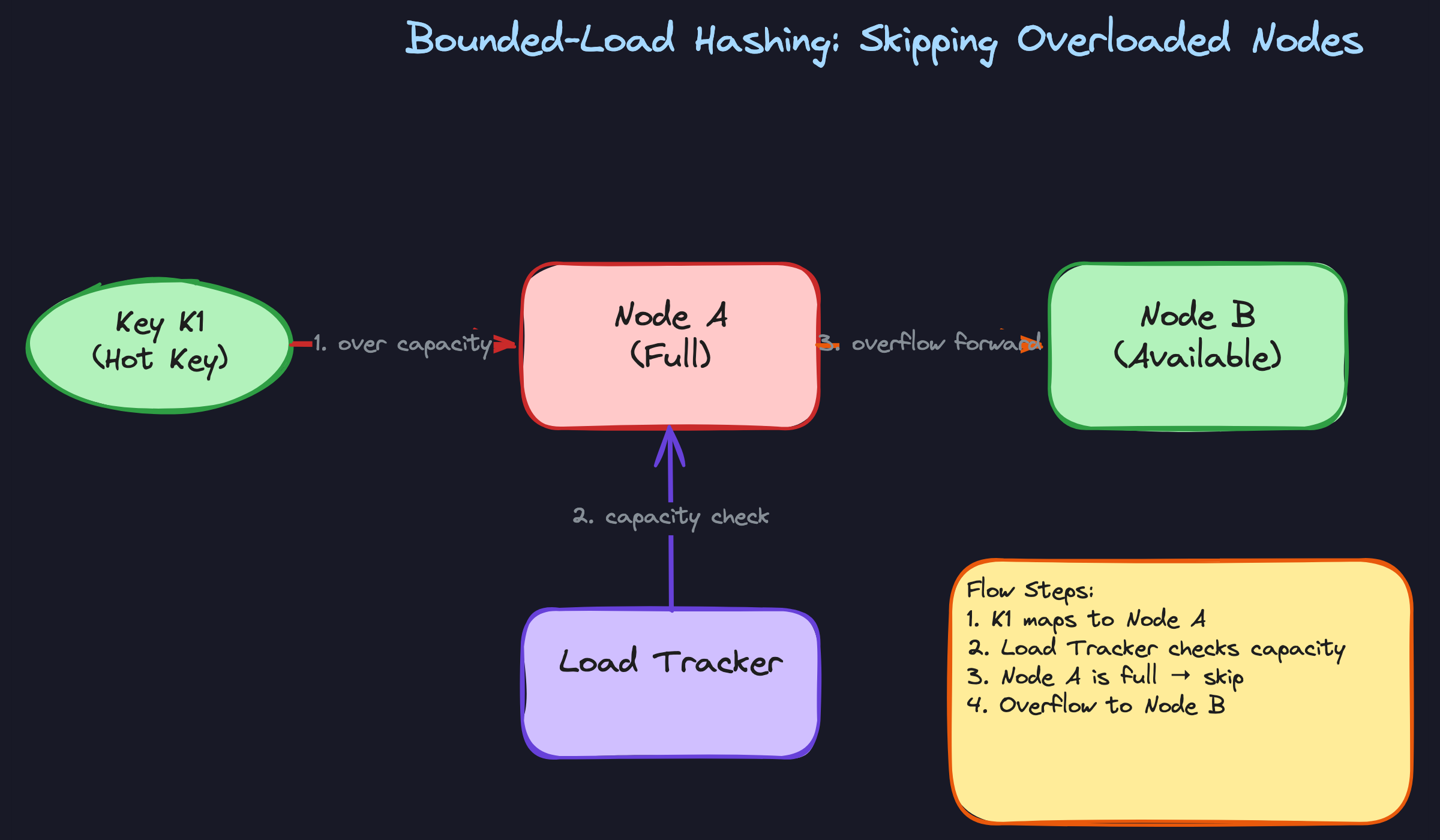
Bounded-Load Consistent Hashing
Standard consistent hashing distributes keys evenly on average. But averages don't help when one key is a celebrity's profile page getting 100x the reads of everything else. That single hot key still lands on one node, and that node melts.
Google published a refinement where each node has a capacity ceiling, typically set to something like (1 + ε) times the average load, where ε is a small constant like 0.25. When a key walks clockwise and finds its target node already at capacity, it keeps walking to the next node. The load tracker enforces this in real time. The elegant part is that when the hot spike subsides, keys naturally settle back to their original positions because the capacity check passes again. You get the stability of consistent hashing during normal operation and graceful spillover during spikes.
When to reach for this: when the interviewer pushes on hot keys or uneven access patterns. If someone asks "what happens if one product goes viral?", bounded-load hashing is a strong answer at the infrastructure layer (alongside application-level caching or key splitting).
Weighted Nodes
Not every server in your fleet is identical. Maybe you just added a rack of machines with twice the RAM, or you're running a mixed cluster where some nodes have SSDs and others don't. You want the beefier machines to handle a proportionally larger share of keys.
The fix is simple and doesn't require changing the algorithm at all. Give the more powerful server more virtual nodes. If Server A has 64 GB of RAM and Server B has 128 GB, give B twice as many vnodes. It naturally absorbs roughly twice the key space. When you need to rebalance after a hardware upgrade, you just adjust the vnode count for that server and let the ring redistribute the minimal set of affected keys.
When to reach for this: any time the interviewer mentions heterogeneous hardware, or when you're designing a system that might run across different instance types in the cloud.
| Pattern | What It Solves | Overhead | When to Mention |
|---|---|---|---|
| Virtual Nodes | Uneven key distribution across physical servers | Larger ring metadata table per client/router | Always; it's the default |
| Replication on Ring | Single point of failure for data | Extra writes per key; must skip same-physical-server vnodes | Any durable storage or database design |
| Bounded-Load Hashing | Hot keys overwhelming a single node | Real-time load tracking per node | When interviewer probes hot-key or viral-content scenarios |
| Weighted Nodes | Heterogeneous server capacity | More vnodes to manage for larger servers | When the fleet isn't uniform hardware |
For most interview problems, you'll default to virtual nodes plus replication on the ring. Those two together cover 90% of what interviewers want to hear. Reach for bounded-load hashing when the conversation turns to hot keys or skewed access patterns, and mention weighted nodes when the design involves mixed hardware or cloud instances of different sizes. You rarely need all four in one answer, but knowing they exist lets you respond precisely to whatever direction the interviewer takes.
What Trips People Up
Here's where candidates lose points, and it's almost always one of these.
The Mistake: Jumping Straight to the Ring
This is the most common one. The interviewer asks "how would you distribute data across these cache nodes?" and the candidate immediately says "we'd use consistent hashing with a ring." Then they start drawing circles and arrows without ever explaining what problem they're solving.
The interviewer is left thinking: do they actually understand why, or did they just memorize a technique?
What this sounds like: "So we hash the servers onto a ring, and each key walks clockwise to find its server." Technically correct. But you skipped the entire motivation, which is the part that demonstrates real understanding.
That setup takes seconds and completely changes how the interviewer perceives your answer. You're not reciting an algorithm. You're solving a problem.
The Mistake: Claiming Consistent Hashing Solves Hot Keys
Interviewers love this follow-up. You've just explained how consistent hashing distributes keys evenly across nodes, and they ask: "What if one particular key gets 100x more traffic than anything else?" A surprising number of candidates say something like "the virtual nodes will spread the load."
No. Virtual nodes spread keys more evenly across servers. They do nothing for a single key that's getting hammered. If a celebrity's profile is being read 50,000 times per second, all 50,000 requests go to whichever node owns that key. Virtual nodes don't change that.
What to say instead: acknowledge the limitation directly. "Consistent hashing balances key ownership, but it can't help when a single key is hot. For that, we'd need something at the application layer, like splitting the hot key across multiple sub-keys (e.g., celebrity_profile_1 through celebrity_profile_10 and reading from a random one), or using bounded-load consistent hashing where overloaded nodes deflect keys to the next available neighbor."
That answer shows you understand the boundary of what the algorithm can and can't do.
The Mistake: Treating Virtual Nodes as a Free Lunch
A candidate explains virtual nodes, the interviewer nods, and then asks "how many virtual nodes would you use?" The weak answer: "A lot. Maybe a thousand per server. More is better for balance."
More is not always better. Every virtual node is an entry in the ring's lookup table. If you have 50 physical servers and 1,000 vnodes each, that's 50,000 entries that every client (or every routing proxy) needs to store in memory and binary-search through on every request. In systems where the ring metadata is gossiped between nodes, more vnodes means more gossip traffic and slower convergence when the topology changes.
Cassandra learned this the hard way. Their original default of 256 vnodes per node caused real operational pain during cluster rebalancing, and they've since moved toward lower vnode counts and even explored single-token-per-node assignments for some workloads.
That single sentence signals you think about operational cost, not just algorithmic elegance.
The Mistake: Explaining the Algorithm in a Vacuum
This one is subtle and it costs senior candidates the most. You deliver a textbook-perfect explanation of consistent hashing: the ring, clockwise walks, virtual nodes, minimal disruption. The interviewer says "great" and moves on. You got zero credit for system design judgment.
The problem is that you never connected it back to the actual system you're building. You explained how consistent hashing works without explaining what it means for your design.
What this sounds like: "Each key walks clockwise to the nearest node, and when a node is removed, only its keys remap." Correct, but abstract.
What it should sound like: "So when one of our Memcached nodes crashes at 2 AM, only about 25% of our cached items need to re-fetch from the database. The other three nodes keep serving hits normally. We get a temporary spike in DB load, not a full cache stampede."
See the difference? The second version tells the interviewer you understand the consequence for the system you're designing. It turns an algorithm explanation into a design decision. Every time you introduce a technique, land it with a concrete "which means for our system..." statement. That's what separates a good answer from one that actually moves the interview forward.
How to Talk About This in Your Interview
You understand the hash ring. You know why virtual nodes matter. None of that helps if you fumble the delivery when the interviewer is staring at you across a whiteboard. This section is about timing, phrasing, and reading the room.
When to Bring It Up
Don't wait for the interviewer to say "consistent hashing." They almost never will. Instead, listen for these cues:
- "How would you distribute data across these nodes?" This is the most direct signal. Any mention of sharding, partitioning, or splitting data across servers is your opening.
- "What happens if one of these servers goes down?" They're probing for fault tolerance. Start with the impact (cache miss storm, data unavailability), then introduce the ring as your solution for minimal disruption.
- "We need to scale from 5 to 50 nodes." Whenever the node count is dynamic, you need a distribution strategy that doesn't blow up during scaling events.
- "How do you avoid hot spots?" This one is sneakier. They might be asking about load balancing at the application layer, but if you're designing a cache or a distributed store, consistent hashing with virtual nodes is the right tool.
- "How does the cache layer handle adding capacity?" Anything about caches growing or shrinking. This is where modular hashing falls apart and you get to explain why.
The general rule: if your architecture has a set of nodes that could change in size and you need to decide which node owns which piece of data, bring it up yourself. Proactively introducing it signals that you've built or operated real distributed systems.
Sample Dialogue
Here's how a strong candidate weaves consistent hashing into a cache design conversation. Notice the candidate doesn't lecture. They respond to the problem first, then name the technique.
Notice what happened: the candidate never said "let me explain consistent hashing." They diagnosed the problem, showed why the naive approach fails, and let the solution emerge naturally. The interviewer kept pushing, and each answer went one layer deeper.
Follow-Up Questions to Expect
"How do you handle replication with consistent hashing?" Walk clockwise past the primary node and place replicas on the next N distinct physical nodes. Emphasize "distinct physical" because with virtual nodes, the next position on the ring might belong to the same machine.
"What about hot keys? One celebrity's profile getting millions of reads?" Consistent hashing distributes keys evenly on average, but a single viral key still lands on one node. Your answer is either bounded-load hashing (the key overflows to the next available node) or application-level splitting (break the hot key into sub-keys like celebrity_profile:shard_1, celebrity_profile:shard_2).
"How is this different from rendezvous hashing?" In rendezvous hashing, each key computes a score against every node and picks the highest. It achieves similar minimal-disruption properties but requires O(N) computation per lookup instead of O(log N) with a sorted ring. Only explain this if asked directly.
"How does Cassandra/DynamoDB actually implement this?" They use token ranges. Instead of hashing each server to random points, the ring is divided into contiguous ranges and each node owns a range. Virtual nodes in Cassandra (called vnodes) mean each node owns multiple small ranges. Mentioning this shows you've gone beyond the textbook.
What Separates Good from Great
- A mid-level answer explains the hash ring and virtual nodes clearly, draws it on the whiteboard, and shows that only ~1/N of keys move when a node changes. This is solid and sufficient for most interviews.
- A senior answer connects the mechanism back to the specific system being designed. Instead of explaining the algorithm in a vacuum, you say something like "so when we add a new cache server to handle the holiday traffic spike, only about 20% of cached items go cold, and those misses are spread across all the remaining servers rather than slamming the database." You also proactively address replication placement and the vnode memory tradeoff without being prompted.
- A staff-level answer brings in operational nuance. You mention that ring rebalancing during node additions should be throttled to avoid saturating the network. You discuss how bounded-load hashing handles the hot-partition problem. You might note that some systems (like Cassandra) have moved away from random token assignment toward algorithmic token placement for more predictable splits. This level of depth signals you've actually run these systems in production.
One whiteboard tip that applies at every level: draw the ring early. Label three or four nodes. Hash a key and physically trace the clockwise path with your marker. Then erase a node and show what moves. That ten-second visual does more convincing than two minutes of verbal explanation ever could.


